search for solutions by category, industries, insights, and people.
.jpg)

In 2025, nearly one quarter of cybersecurity incidents were caused by misconfigured IT or cloud security settings, a risk that continues to grow as organizations rely more heavily on SaaS platforms like Microsoft 365.
As cloud adoption accelerates, the attack surface expands, often outpacing the ability of security teams to keep configurations aligned with best practices. The result is a growing gap between how cloud environments change and how often their security settings are formally reviewed.
That reality sits at the center of a recent alert from the Cybersecurity and Infrastructure Security Agency (CISA), which warned that improper Microsoft 365 configurations have already led to real world compromises, including a cyberattack against a healthcare organization triggered by cloud misconfiguration. Healthcare organizations, in particular, remain prime targets for cybercrime.
Cloud platforms change faster than most organizations’ governance, audit, and risk management cycles. New features, default settings, and security controls are released continuously, often without leadership awareness or formal review.
Industry research shows that more than half of cloud breaches are linked to configuration drift over time. These issues don’t arise because cloud providers are insecure. They arise because configuration decisions are often:
Over time, small gaps compound into meaningful exposure.
Microsoft 365 is embedded in daily operations for most organizations. Email, file sharing, collaboration, identity management, and data storage all live within a single ecosystem, making it both powerful and vulnerable.
CISA has emphasized that improper configuration of cloud security controls has already resulted in actual compromises, prompting federal mandates to harden Microsoft 365 environments using secure configuration baselines.
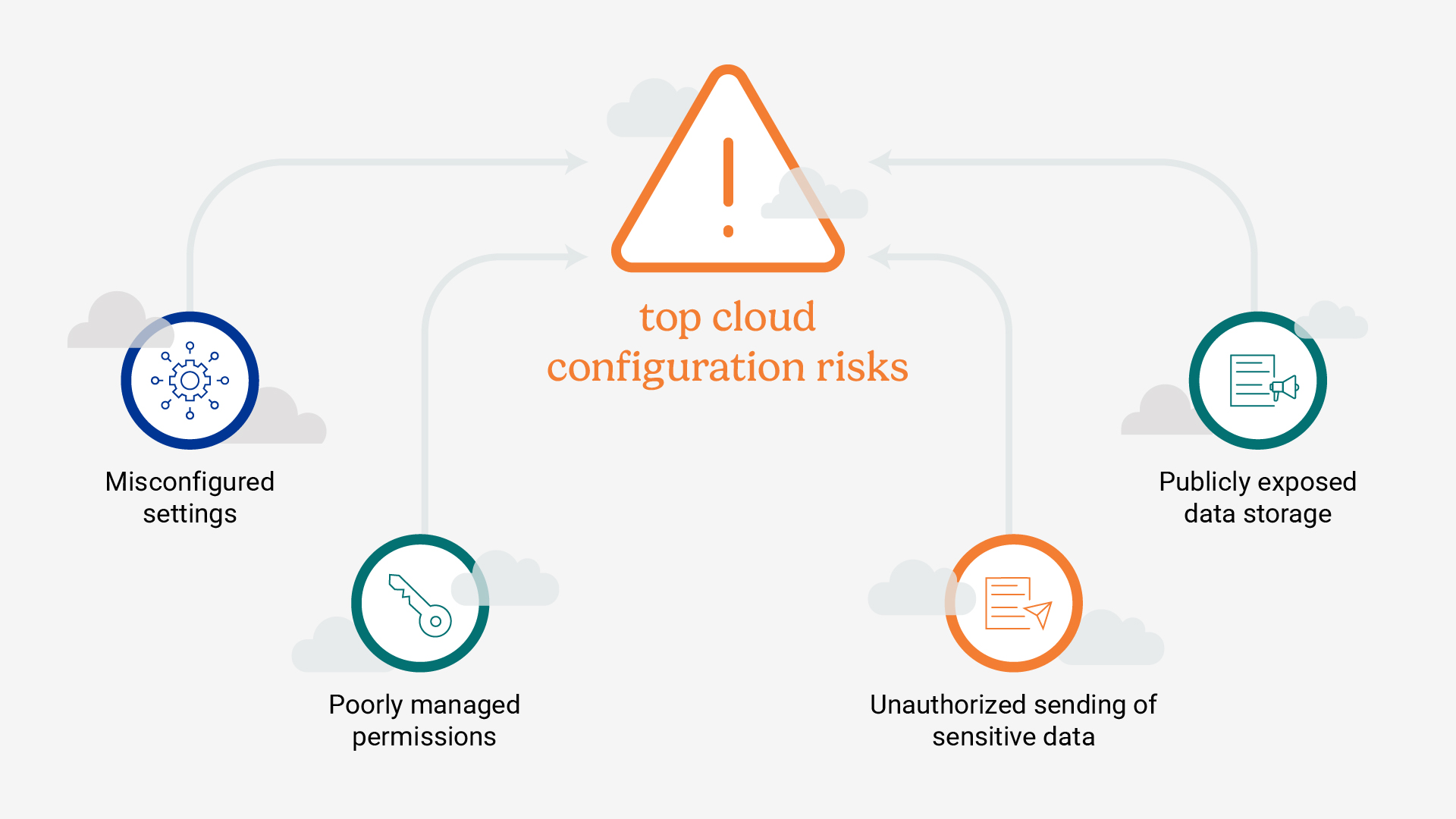
Key risk factors include:
For many organizations, Microsoft 365 contains their most sensitive data, yet its security posture has never been independently evaluated.
A cloud security evaluation focuses specifically on how cloud services are configured today, not how policies are written or whether controls exist on paper.
An independent third-party team performs cloud security evaluations by comparing an organization’s Microsoft 365 (and other cloud platforms such as Azure, AWS, and Google Cloud) against Center for Internet Security (CIS) benchmarks, which reflect consensus driven best practices developed by the global cybersecurity community.
CIS Benchmarks are publicly available, regularly updated, and widely regarded as the industry standard for secure configuration across major technologies.
A typical cloud security evaluation includes:
Engagements are efficient, often requiring only one to two days of technical review, and culminate in a leadership ready report.
Evaluations frequently uncover settings that were never intentionally chosen by leadership, including:
For organizations operating under privacy regulations, such as healthcare entities or businesses subject to California privacy laws, these gaps can create compliance exposure alongside cyber risk.
As cloud platforms introduce new capabilities and settings on a regular basis, security configurations should be revisited with similar discipline. We recommend:
While internal IT teams should regularly reassess configurations, periodic external evaluations provide leadership with an objective view of current exposure and help determine which issues deserve immediate attention. Without these reviews, unexamined cloud configurations can increase security risk.
Elliott Davis helps organizations take a more disciplined approach to cybersecurity by providing independent, practical assessments of cloud and technology risk. Our services include:
Together, these services help organizations move beyond point in time visibility to a more consistent approach to identifying, prioritizing, and addressing risk. Our cloud security evaluations give leadership an objective view of current configurations, highlight gaps against recognized best practices, and outline clear, actionable steps to reduce exposure before issues become incidents.
Contact us today to get started.
The information provided in this communication is of a general nature and should not be considered professional advice. You should not act upon the information provided without obtaining specific professional advice. The information above is subject to change.